Prompt Details
Model
(claude-4-6-sonnet)
Token size
4,155
Example input
[CONSTRAINTS_DOCUMENT]: ```text Finance Fabric Governance Working Session — 2026-03-14 - All production financial reporting workspaces must remain on F256 capacity until SAP migration completes. - CAB approval is required before enabling Copilot features in any finance-associated workspace. - External guest sharing is prohibited for all gold-tier workspaces. - Bronze-tier workspaces may use Fabric Git integration if connected to Azure DevOps only. - Current concern: several legacy SSRS datasets still refresh through on-prem gateway. - Security team stated that workspace-admin rights must not be assigned directly to individuals. - Pending decision: whether Fabric Data Activator can be enabled tenant-wide. - Existing Power BI deployment pipelines will remain active until Q4. - Some teams requested GitHub Enterprise integration, but architecture review has not approved it. - Data retention policy requires 7-year archive preservation for finance datasets. - Multiple workspaces currently exceed documented ownership limits. ---DOCUMENT-BREAK--- CAB Minutes — 2026-03-21 - F64 Sandbox capacity approved for experimentation only. - No production PII data allowed in Sandbox capacities. - All production semantic models require source control before migration wave 2. - Tenant-level sharing links currently disabled due to audit findings.
[ARCHITECTURAL_ARTEFACT]: ```text CAPACITY INVENTORY - F256-PROD-FINANCE → assigned to FIN-GLD-REPORTING, FIN-EXEC-DASH - F128-ANALYTICS → assigned to SILVER-OPS, SILVER-HR - F64-SANDBOX → assigned to DEV-PLAYGROUND WORKSPACE INVENTORY - FIN-GLD-REPORTING | tier=gold | manager=Sarah Chen - FIN-EXEC-DASH | tier=gold | manager=unknown - SILVER-OPS | tier=silver | manager=David Ali - DEV-PLAYGROUND | tier=bronze AD GROUPS - FABRIC_FINANCE_ADMINS - FABRIC_FINANCE_VIEWERS - FABRIC_SANDBOX_USERS SOURCE CONTROL - Azure DevOps connected for SILVER-OPS - No source control configured for FIN-EXEC-DASH PIPELINES - Finance-Prod-Pipeline → prod only - Legacy-PBI-Deploy → active ```
[PROJECT_SCOPE]: Finance reporting modernization — migration wave 2
Example output
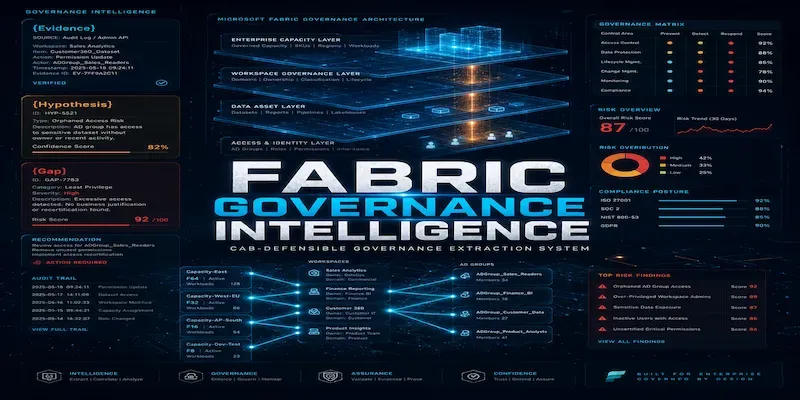
# FABRIC GOVERNANCE INTELLIGENCE PACKAGE
## Finance Reporting Modernization — Migration Wave 2
### Analysis Date: 2026-05-05 | Scope: Finance Reporting Modernization — Migration Wave 2
---
# PHASE 1: ENTITY INVENTORY EXTRACTION
## ENTITIES.CAPACITIES
- **F256-PROD-FINANCE** | size: F256 | status: assigned | scope: FIN-GLD-REPORTING, FIN-EXEC-DASH | tag: {Evidence: Architectural Artefact — Capacity Inventory, row 1}
- **F128-ANALYTICS** | size: F128 | status: assigned | scope: SILVER-OPS, SILVER-HR | tag: {Evidence: Architectural Artefact — Capacity Inventory, row 2}
> Note: SILVER-HR workspace appears in capacity assignment but is absent from Workspace Inventory. See G-001.
- **F64-SANDBOX** | size: F64 | status: assigned | scope: DEV-PLAYGROUND | tag: {Evidence: Architectural Artefact — Capacity Inventory, row 3; CAB Minutes — 2026-03-21, item 1}
---
## ENTITIES.WORKSPACES
- **FIN-GLD-REPORTING** | tier: gold | dependencies: F256-PROD-FINANCE, Finance-Prod-Pipeline, legacy SSRS on-prem gateway (stated concern) | manager: Sarah Chen | tag: {Evidence: Architectural Artefact — Workspace Inventory, row 1; Governance Working Session — 2026-03-14, item 6}
- **FIN-EXEC-DASH** | tier: gold | dependencies: F256-PROD-FINANCE | manager: unknown | tag: {Evidence: Architectural Artefact — Workspace Inventory, row 2; Architectural Artefact — Source Control section}
> Source control not configured. See G-002.
- **SILVER-OPS** | tier: silver | dependencies: F128-ANALYTICS, Azure DevOps source control | manager: David Ali | tag: {Evidence: Architectural Artefact — Workspace Inventory, row 3; Architectural Artefact — Source Control section}
- **DEV-PLAYGROUND** | tier: bronze | dependencies: F64-SANDBOX | manager: unknown | tag: {Evidence: Architectural Artefact — Workspace Inventory, row 4}
> Manager not stated. See G-003.
- **SILVER-HR** | tier: {Gap: needs-input — tier not stated in Workspace Inventory, only referenced in Capacity Inventory} | dependencies: F128-ANALYTICS | manager: unknown | tag: {Gap: G-001 — workspace present in capacity assignment but absent from Workspace Inventory}
---
## ENTITIES.AD_GROUPS
- **FABRIC_FINANCE_ADMINS** | scope: admin | environments: {Gap: not stated — no explicit environment mapping provided} | tag: {Evidence: Architectural Artefact — AD Groups, row 1}
- **FABRIC_FINANCE_VIEWERS** | scope: viewer | environments: {Gap: not stated} | tag: {Evidence: Architectural Artefact — AD Groups, row 2}
- **FABRIC_SANDBOX_USERS** | scope: {Hypothesis: contributor or viewer-level access scoped to DEV-PLAYGROUND — the only sandbox capacity listed; Premise: group name includes "SANDBOX"; Premise: only one sandbox capacity exists (F64-SANDBOX); Conclusion: group almost certainly scoped to DEV-PLAYGROUND} | environments: dev/sandbox | tag: {Evidence: Architectural Artefact — AD Groups, row 3; Hypothesis: H-001}
---
## ENTITIES.FEATURES
- **Copilot** | enablement-level: workspace or capacity (not yet determined) | current-state: pending — CAB approval required before enabling in any finance-associated workspace | tag: {Evidence: Governance Working Session — 2026-03-14, item 2}
- **Fabric Git Integration** | enablement-level: workspace | current-state: partially active — enabled for SILVER-OPS via Azure DevOps; not configured for FIN-EXEC-DASH, DEV-PLAYGROUND, FIN-GLD-REPORTING | tag: {Evidence: Architectural Artefact — Source Control section; Governance Working Session — 2026-03-14, item 4}
> Bronze-tier constraint limits Git integration to Azure DevOps only. Gold-tier constraint not explicitly stated for Git. See G-004.
- **Fabric Data Activator** | enablement-level: tenant (proposed) | current-state: pending — decision not made | tag: {Evidence: Governance Working Session — 2026-03-14, item 7}
- **Tenant-Level Sharing Links** | enablement-level: tenant | current-state: off — disabled following audit findings | tag: {Evidence: CAB Minutes — 2026-03-21, item 4}
- **External Guest Sharing** | enablement-level: workspace (gold-tier specific prohibition) | current-state: prohibited for gold-tier workspaces; state for silver/bronze unstated | tag: {Evidence: Governance Working Session — 2026-03-14, item 3}
- **GitHub Enterprise Integration** | enablement-level: tenant or workspace | current-state: prohibited — architecture review not approved | tag: {Evidence: Governance Working Session — 2026-03-14, item 9}
- **Legacy SSRS / On-Prem Gateway Refresh** | enablement-level: workspace/dataset | current-state: active — several legacy SSRS datasets still refresh through on-prem gateway | tag: {Evidence: Governance Working Session — 2026-03-14, item 5}
---
## ENTITIES.PIPELINES_AND_REPOS
- **Finance-Prod-Pipeline** | type: Fabric deployment pipeline | environments: prod | migration-required: {Hypothesis: yes — wave 2 migration scope, and all production semantic models require source control before wave 2; H-002} | tag: {Evidence: Architectural Artefact — Pipelines section, row 1}
- **Legacy-PBI-Deploy** | type: Power BI deployment pipeline (fabric-builtin or standalone) | environments: {Gap: not stated — likely prod given "legacy" label and no environment qualifier; G-005} | migration-required: no — explicitly stated to remain active until Q4 | tag: {Evidence: Governance Working Session — 2026-03-14, item 8; Architectural Artefact — Pipelines section, row 2}
- **Azure DevOps (SILVER-OPS repo)** | type: Azure DevOps | environments: silver | migration-required: no — already connected | tag: {Evidence: Architectural Artefact — Source Control section, row 1}
---
## ENTITIES.STAKEHOLDER_ROLES
- **Sarah Chen** | accountability: FIN-GLD-REPORTING workspace management | tag: {Evidence: Architectural Artefact — Workspace Inventory, row 1}
- **David Ali** | accountability: SILVER-OPS workspace management | tag: {Evidence: Architectural Artefact — Workspace Inventory, row 3}
- **Security Team** | accountability: workspace admin assignment policy | tag: {Evidence: Governance Working Session — 2026-03-14, item 6}
- **CAB (Change Advisory Board)** | accountability: Copilot enablement approval; production semantic model source control gate; F64-SANDBOX usage boundaries | tag: {Evidence: Governance Working Session — 2026-03-14, item 2; CAB Minutes — 2026-03-21, items 1, 3}
- **Architecture Review Board** | accountability: GitHub Enterprise integration approval | tag: {Evidence: Governance Working Session — 2026-03-14, item 9}
- **FIN-EXEC-DASH manager** | accountability: FIN-EXEC-DASH workspace governance | tag: {Gap: G-002 — manager not identified in any input document}
---
# PHASE 2: CONSTRAINT MATRIX
## CONSTRAINTS.LOCKED
**L-001** — All production financial reporting workspaces must remain on F256 capacity until SAP migration completes.
- Source: {Evidence: Governance Working Session — 2026-03-14, item 1}
- Affected entities: FIN-GLD-REPORTING, FIN-EXEC-DASH, F256-PROD-FINANCE
- Implication: No capacity rebalancing, downsizing, or reassignment of gold-tier finance workspaces is permitted during the SAP migration window.
**L-002** — Workspace admin rights must not be assigned directly to individuals.
- Source: {Evidence: Governance Working Session — 2026-03-14, item 6 — Security team stated}
- Affected entities: All workspaces; AD groups FABRIC_FINANCE_ADMINS
- Implication: Admin access must route through AD groups exclusively; any direct individual assignment is a security policy violation.
**L-003** — Tenant-level sharing links are disabled.
- Source: {Evidence: CAB Minutes — 2026-03-21, item 4}
- Affected entities: All workspaces at tenant level
- Implication: No sharing-link-based content distribution is available across the tenant; sharing must occur through workspace membership or app distribution.
**L-004** — External guest sharing is prohibited for all gold-tier workspaces.
- Source: {Evidence: Governance Working Session — 2026-03-14, item 3}
- Affected entities: FIN-GLD-REPORTING, FIN-EXEC-DASH
- Implication: No B2B/guest access can be granted to either gold workspace regardless of capacity or AD group membership.
**L-005** — All production semantic models require source control before migration wave 2.
- Source: {Evidence: CAB Minutes — 2026-03-21, item 3}
- Affected entities: FIN-GLD-REPORTING, FIN-EXEC-DASH, Finance-Prod-Pipeline
- Implication: FIN-EXEC-DASH has no source control configured; this is a blocking gate for wave 2 migration. FIN-GLD-REPORTING source control status is also unconfirmed. See G-004.
**L-006** — Data retention policy requires 7-year archive preservation for finance datasets.
- Source: {Evidence: Governance Working Session — 2026-03-14, item 10}
- Affected entities: FIN-GLD-REPORTING, FIN-EXEC-DASH, all finance-associated datasets
- Implication: Dataset deletion, workspace decommission, or storage migration for finance data requires validated 7-year archive before execution.
**L-007** — No production PII data allowed in Sandbox capacities.
- Source: {Evidence: CAB Minutes — 2026-03-21, item 2}
- Affected entities: F64-SANDBOX, DEV-PLAYGROUND, FABRIC_SANDBOX_USERS
- Implication: Any test or development activity using real finance PII data is prohibited in DEV-PLAYGROUND; synthetic or masked datasets are required.
**L-008** — Existing Power BI deployment pipelines remain active until Q4.
- Source: {Evidence: Governance Working Session — 2026-03-14, item 8}
- Affected entities: Legacy-PBI-Deploy
- Implication: Legacy-PBI-Deploy cannot be decommissioned or redirected before Q4; wave 2 migration planning must operate in parallel with it.
---
## CONSTRAINTS.PERMITTED
**P-001** — F64-SANDBOX capacity is approved for experimentation only.
- Source: {Evidence: CAB Minutes — 2026-03-21, item 1}
- Conditions: Experimentation must not involve production PII data (see L-007).
**P-002** — Bronze-tier workspaces may use Fabric Git integration if connected to Azure DevOps only.
- Source: {Evidence: Governance Working Session — 2026-03-14, item 4}
- Conditions: Azure DevOps must be the Git provider; GitHub Enterprise is not approved (see PROHIBITED section).
---
## CONSTRAINTS.PROHIBITED
**PR-001** — GitHub Enterprise integration is not approved.
- Source: {Evidence: Governance Working Session — 2026-03-14, item 9}
- Workaround-allowed: unstated — architecture review has not approved; requests were made but rejected at current stage.
**PR-002** — External guest sharing prohibited in gold-tier workspaces (see L-004 — duplicated here for completeness of PROHIBITED register).
- Source: {Evidence: Governance Working Session — 2026-03-14, item 3}
- Workaround-allowed: no — stated as an absolute prohibition with no workaround mentioned.
**PR-003** — Direct individual assignment of workspace admin rights prohibited (see L-002).
- Source: {Evidence: Governance Working Session — 2026-03-14, item 6}
- Workaround-allowed: no — must route through AD groups.
---
## CONSTRAINTS.PENDING
**PD-001** — Copilot features: CAB approval required before enabling in any finance-associated workspace.
- Source: {Evidence: Governance Working Session — 2026-03-14, item 2}
- Pending-approver: CAB
- Blocking-impact: Copilot cannot be activated in FIN-GLD-REPORTING, FIN-EXEC-DASH, or any other finance-associated workspace until CAB grants approval; wave 2 roadmap cannot include Copilot activation for finance scope.
**PD-002** — Fabric Data Activator tenant-wide enablement: decision pending.
- Source: {Evidence: Governance Working Session — 2026-03-14, item 7}
- Pending-approver: unstated
- Blocking-impact: Data Activator cannot be scoped into wave 2 feature rollout until this decision resolves; downstream alerting or event-driven patterns dependent on Data Activator are blocked.
**PD-003** — Source control for FIN-GLD-REPORTING and FIN-EXEC-DASH: required before wave 2 (L-005), but configuration is absent or unconfirmed.
- Source: {Evidence: CAB Minutes — 2026-03-21, item 3; Architectural Artefact — Source Control section}
- Pending-approver: CAB (wave 2 gate) / workspace managers (Sarah Chen for FIN-GLD-REPORTING; unknown for FIN-EXEC-DASH)
- Blocking-impact: Wave 2 migration cannot proceed for either gold-tier workspace until source control is configured and validated.
---
## CONSTRAINTS.AMBIGUOUS
**AM-001** — Git integration constraint for bronze-tier (P-002) is stated, but no equivalent constraint is stated for gold or silver tiers.
- Source: {Evidence: Governance Working Session — 2026-03-14, item 4}
- Ambiguity: Does the Azure DevOps-only requirement apply to silver and gold tiers, or only bronze? The constraint language scopes to "bronze-tier workspaces" exclusively.
- {Hypothesis H-003: The Azure DevOps-only requirement likely applies across all tiers given that GitHub Enterprise is explicitly not approved (PR-001). Premise: GitHub Enterprise is the only named alternative Git provider in the inputs. Premise: It has not been approved at architecture review. Conclusion: No Git provider other than Azure DevOps is available for any tier. This would make the bronze-tier language a subset of a broader implied constraint rather than a bronze-specific carve-out.}
- Recommend-clarification: yes
**AM-002** — Multiple workspaces currently exceed documented ownership limits.
- Source: {Evidence: Governance Working Session — 2026-03-14, item 11}
- Ambiguity: "Documented ownership limits" are not defined in any input; the workspaces in violation are not named; the consequence of exceeding limits is not stated.
- {Hypothesis H-004: FIN-EXEC-DASH is among the violating workspaces because its manager field is "unknown" in the Architectural Artefact, suggesting absent or unassigned ownership. Premise: FIN-EXEC-DASH has no stated manager. Premise: The constraint cites multiple workspaces exceeding ownership limits. Conclusion: Unmanaged workspaces are the most likely candidates for ownership limit violations. Confidence: Medium.}
- Recommend-clarification: yes
**AM-003** — Legacy SSRS datasets refreshing through on-prem gateway — no constraint is stated regarding their disposition or migration timeline.
- Source: {Evidence: Governance Working Session — 2026-03-14, item 5 — cited as "current concern" only}
- Ambiguity: Whether these datasets must be migrated before wave 2, whether they can coexist with Fabric semantic models, and which workspaces host them is unstated.
- {Hypothesis H-005: These datasets likely reside in FIN-GLD-REPORTING given it is the primary production financial reporting workspace, and the concern was raised in a finance governance session. Premise: The session is finance-scoped. Premise: FIN-GLD-REPORTING is the gold-tier production finance reporting workspace. Conclusion: On-prem gateway dependency most likely attaches to FIN-GLD-REPORTING. Confidence: Medium.}
- Recommend-clarification: yes
---
## CONSTRAINTS.IMPLIED
**IM-001** — SILVER-HR workspace must exist as a governed entity even though it is absent from the Workspace Inventory.
- {Hypothesis H-006: SILVER-HR is an active, assigned workspace. Premise: F128-ANALYTICS capacity assigns SILVER-HR explicitly. Premise: Capacity assignments in Fabric require a workspace to exist. Conclusion: SILVER-HR exists in the tenant but was omitted from the Workspace Inventory document, likely due to documentation gap rather than decommission.}
- Confidence: High
- Risk-if-wrong: If SILVER-HR is decommissioned, F128-ANALYTICS capacity assignment data is stale and the capacity inventory is inaccurate, which invalidates capacity risk calculations.
**IM-002** — DEV-PLAYGROUND is the only bronze-tier workspace in scope; therefore all bronze-tier constraints apply solely to DEV-PLAYGROUND within this wave.
- {Hypothesis H-007: Premise: DEV-PLAYGROUND is the only bronze-tier workspace listed. Premise: No other bronze-tier workspaces are named in any input. Conclusion: Bronze-tier constraints (P-002) map exclusively to DEV-PLAYGROUND for wave 2 scope.}
- Confidence: High
- Risk-if-wrong: If additional bronze-tier workspaces exist outside the inventory, they inherit the same Git constraint and are ungoverned by the current framework.
**IM-003** — FABRIC_FINANCE_ADMINS must be the AD group through which admin rights to FIN-GLD-REPORTING and FIN-EXEC-DASH are granted, given L-002 prohibits direct individual assignment.
- {Hypothesis H-008: Premise: L-002 mandates admin rights route through AD groups only. Premise: FABRIC_FINANCE_ADMINS is the only finance-scoped admin group in the AD group inventory. Conclusion: This group is the designated admin access vehicle for gold-tier finance workspaces.}
- Confidence: High
- Risk-if-wrong: If direct individual assignments currently exist (pre-L-002 enforcement), those assignments represent live security policy violations that must be remediated before wave 2.
---
# PHASE 3: TENANCY SAFE-SETTING FLOOR™ CALCULATION
## CATEGORY 1 — Tenant-Level Fabric Toggles
- **Tenant-level sharing links**: FLOOR = OFF
Reasoning: Disabled following audit findings; re-enabling without CAB review would re-open the audit finding.
Source: {Evidence: CAB Minutes — 2026-03-21, item 4}
- **External guest sharing (gold-tier workspaces)**: FLOOR = OFF (scoped prohibition)
Reasoning: L-004 mandates prohibition; no conditional path to enable exists within inputs.
Source: {Evidence: Governance Working Session — 2026-03-14, item 3}
- **Copilot (finance-associated workspaces)**: FLOOR = OFF pending CAB
Reasoning: PD-001; enabling before CAB approval violates stated governance gate.
Source: {Evidence: Governance Working Session — 2026-03-14, item 2}
- **Fabric Data Activator (tenant-wide)**: FLOOR = OFF pending decision
Reasoning: PD-002; decision not made; enabling preemptively bypasses the pending decision process.
Source: {Evidence: Governance Working Session — 2026-03-14, item 7}
- **GitHub Enterprise integration**: FLOOR = DISABLED
Reasoning: Architecture review has not approved; enabling would constitute an unapproved architecture change.
Source: {Evidence: Governance Working Session — 2026-03-14, item 9}
---
## CATEGORY 2 — Capacity-Level Settings
- **Capacity assignment stability**: FLOOR = no reassignment until SAP migration completes
Per-tier guidance: gold (F256-PROD-FINANCE) = locked; silver (F128-ANALYTICS) = {Hypothesis H-009: no explicit lock stated, but SAP migration lock applies only to gold; silver capacity reassignment appears to be unblocked — Confidence: Medium}; bronze (F64-SANDBOX) = experimentation-only, approved by CAB.
Reasoning: L-001 locks gold-tier capacity; silver and bronze lack equivalent locking constraints in the inputs.
Source: {Evidence: Governance Working Session — 2026-03-14, item 1; CAB Minutes — 2026-03-21, item 1}
- **Sandbox PII segregation**: FLOOR = no production PII data in F64-SANDBOX
Per-tier guidance: bronze (DEV-PLAYGROUND) = synthetic/masked data only; silver and gold = not applicable to sandbox rule.
Reasoning: L-007; violation exposes the organization to data governance and regulatory risk.
Source: {Evidence: CAB Minutes — 2026-03-21, item 2}
---
## CATEGORY 3 — Security & External Connectivity
- **Admin assignment via AD groups only**: FLOOR = no direct individual admin assignments in any workspace
Reasoning: L-002; security team mandated this; any direct assignment is a live violation.
Source: {Evidence: Governance Working Session — 2026-03-14, item 6}
- **On-prem gateway for SSRS datasets**: FLOOR = gateway must remain active until migration path is defined
Reasoning: Several legacy SSRS datasets still depend on the gateway; disabling it would break production refresh cycles in finance workspaces.
Source: {Evidence: Governance Working Session — 2026-03-14, item 5; Hypothesis H-005}
- **7-year archive enforcement for finance datasets**: FLOOR = archive must be validated before any finance dataset is decommissioned, moved, or transformed
Reasoning: L-006; regulatory or policy requirement; no exceptions stated.
Source: {Evidence: Governance Working Session — 2026-03-14, item 10}
---
## CATEGORY 4 — Source Control & CICD
- **Git provider**: FLOOR = Azure DevOps only (GitHub Enterprise blocked)
Reasoning: PR-001 blocks GitHub Enterprise; P-002 permits Azure DevOps for bronze; AM-001 implies Azure DevOps is the only viable provider across all tiers.
Source: {Evidence: Governance Working Session — 2026-03-14, items 4 and 9; Hypothesis H-003}
- **Production semantic model source control gate**: FLOOR = all production semantic models must be source-controlled before wave 2 migration proceeds
Reasoning: L-005; CAB-stated gate. FIN-EXEC-DASH is currently non-compliant.
Source: {Evidence: CAB Minutes — 2026-03-21, item 3}
- **Legacy-PBI-Deploy pipeline**: FLOOR = must remain active and untouched until Q4
Reasoning: L-008; decommissioning before Q4 violates the stated constraint.
Source: {Evidence: Governance Working Session — 2026-03-14, item 8}
---
## CATEGORY 5 — Access & Permissions Floor
- **AD group mandatory for admin access**: FLOOR = FABRIC_FINANCE_ADMINS (and equivalent groups) are the only vehicles for workspace admin assignment
Reasoning: L-002; H-008; direct individual admin rights must be audited and removed.
Source: {Evidence: Governance Working Session — 2026-03-14, item 6; Hypothesis H-008}
- **FABRIC_SANDBOX_USERS scope**: FLOOR = scoped to DEV-PLAYGROUND / F64-SANDBOX only; must not have access to silver or gold workspaces
Reasoning: {Hypothesis H-001 and H-007} — sandbox group should not cross workspace tiers; cross-tier access would violate PII segregation and capacity assignment intent.
Source: {Hypothesis H-001; H-007}
- **Workspace ownership**: FLOOR = every workspace must have an identified owner (AD group or named manager); unmanaged workspaces must be remediated before wave 2
Reasoning: AM-002 identifies ownership violations; L-002 prohibits individual assignments; FIN-EXEC-DASH manager is currently unknown.
Source: {Evidence: Governance Working Session — 2026-03-14, item 11; Architectural Artefact — Workspace Inventory; Hypothesis H-004}
---
## CATEGORY 6 — Change Control Floor
- **CAB approval for Copilot enablement**: FLOOR = CAB approval must precede any Copilot activation in finance scope
Reasoning: PD-001; no path exists to enable without CAB sign-off.
Source: {Evidence: Governance Working Session — 2026-03-14, item 2}
- **CAB gate for wave 2 migration**: FLOOR = source control validation for all production semantic models must be demonstrated to CAB before wave 2 proceeds
Reasoning: L-005 stated as a wave 2 prerequisite in CAB Minutes.
Source: {Evidence: CAB Minutes — 2026-03-21, item 3}
- **Architecture review for new integrations**: FLOOR = any new Git provider or external integration requires architecture review board approval before enablement
Reasoning: PR-001 establishes that the architecture review board is the approval body for integration decisions; no integration should bypass this gate.
Source: {Evidence: Governance Working Session — 2026-03-14, item 9}
---
**TENANCY_SAFE_SETTING_FLOOR_TOTAL: 18 settings**
**Categories with {Hypothesis} dominance:** Category 5 (Access & Permissions Floor — FABRIC_SANDBOX_USERS scope, workspace ownership floor), Category 2 (silver capacity reassignment status)
**Categories with {Gap} requiring input:** Category 3 (on-prem gateway migration path undefined — G-006), Category 4 (source control status of FIN-GLD-REPORTING unconfirmed — G-004), Category 5 (FIN-EXEC-DASH manager unknown — G-002)
---
# PHASE 4: AD GROUP IMPACT CASCADE™
---
## Group: FABRIC_FINANCE_ADMINS
**Current-scope:** Admin access to finance workspaces (FIN-GLD-REPORTING, FIN-EXEC-DASH implied by H-008); exact workspace list not documented in inputs.
**Cascade-on-feature-enable:**
- If **Copilot** enabled at capacity level (F256-PROD-FINANCE) → members of FABRIC_FINANCE_ADMINS gain access to Copilot controls in FIN-GLD-REPORTING and FIN-EXEC-DASH before CAB approval is secured, violating PD-001. {Evidence: Governance Working Session — 2026-03-14, item 2}
- If **Fabric Data Activator** enabled tenant-wide → admin group inherits tenant-level management responsibilities for Data Activator within finance workspaces; scope of accountability expands without a defined governance owner. {Evidence: Governance Working Session — 2026-03-14, item 7; Hypothesis H-010: admin group is the default accountability bearer for new tenant-level features in finance scope}
- If **Git integration** enabled for gold-tier workspaces → FABRIC_FINANCE_ADMINS must configure and maintain repo connections; FIN-EXEC-DASH has no existing source control, so this group must execute the initial configuration. {Evidence: CAB Minutes — 2026-03-21, item 3; Architectural Artefact — Source Control section}
**Cascade-on-feature-disable:**
- If **on-prem gateway** is disabled or decommissioned → SSRS dataset refresh breaks for workspaces under FABRIC_FINANCE_ADMINS governance; admin group owns the incident response. {Hypothesis H-005; Evidence: Governance Working Session — 2026-03-14, item 5}
- If **Legacy-PBI-Deploy** is retired before Q4 → any production deployment dependent on this pipeline breaks; admin group is the first-line responder. {Evidence: Governance Working Session — 2026-03-14, item 8}
**Risk-if-misconfigured:** High — this group controls production financial reporting workspaces on F256; misconfiguration affects FIN-GLD-REPORTING and FIN-EXEC-DASH simultaneously.
**Recommended-pre-rollout-check:** Audit FABRIC_FINANCE_ADMINS membership to confirm no direct individual admin assignments exist outside this group (L-002 compliance), and validate the group has explicit workspace admin assignment in FIN-EXEC-DASH.
**Tags:** {Evidence: Architectural Artefact — AD Groups; Governance Working Session — 2026-03-14, item 6; Hypothesis H-008, H-010}
---
## Group: FABRIC_FINANCE_VIEWERS
**Current-scope:** Viewer access to finance workspaces; exact workspace list not documented.
**Cascade-on-feature-enable:**
- If **tenant-level sharing links** re-enabled → viewer-level users could potentially share content externally or distribute links beyond the intended audience, widening the exposure surface for finance reports. {Evidence: CAB Minutes — 2026-03-21, item 4}
- If **Copilot** enabled in finance workspaces → viewers may gain access to Copilot-generated summaries or Q&A over finance data depending on how Copilot access is scoped (workspace-level vs. per-item); scope of data exposure to viewers increases. {Hypothesis H-011: Copilot access in Fabric can expose AI-generated outputs to workspace members including viewers; Premise: viewer membership is not restricted in inputs; Confidence: Medium}
- If **External guest sharing** enabled in gold-tier (currently prohibited under L-004) → FABRIC_FINANCE_VIEWERS could be misconfigured to include external guest accounts, violating the gold-tier prohibition. {Evidence: Governance Working Session — 2026-03-14, item 3}
**Cascade-on-feature-disable:**
- If **tenant-level sharing links** remain off → no impact on FABRIC_FINANCE_VIEWERS' ability to access workspaces directly; access routes through workspace membership remain intact. {Evidence: CAB Minutes — 2026-03-21, item 4}
**Risk-if-misconfigured:** Medium — viewers cannot modify data but can access and potentially extract sensitive financial reports; PII exposure risk if guest accounts are added to this group.
**Recommended-pre-rollout-check:** Audit FABRIC_FINANCE_VIEWERS membership for any external guest accounts; confirm the group is not assigned to DEV-PLAYGROUND or SILVER-OPS (cross-tier access not documented but not explicitly prohibited).
**Tags:** {Evidence: Architectural Artefact — AD Groups; Hypothesis H-011}
---
## Group: FABRIC_SANDBOX_USERS
**Current-scope:** {Hypothesis H-001} Scoped to DEV-PLAYGROUND / F64-SANDBOX for experimentation.
**Cascade-on-feature-enable:**
- If **Fabric Git integration** enabled for DEV-PLAYGROUND (bronze-tier, Azure DevOps) → FABRIC_SANDBOX_USERS can push/pull to connected Azure DevOps repo; risk of committing non-anonymized test data to source control if PII segregation is not enforced at the dataset level. {Evidence: Governance Working Session — 2026-03-14, item 4; CAB Minutes — 2026-03-21, item 2}
- If **Fabric Data Activator** enabled tenant-wide → FABRIC_SANDBOX_USERS gain access to Data Activator in DEV-PLAYGROUND; experimentation with event-driven patterns becomes possible; no production risk if L-007 PII constraint is enforced. {Evidence: Governance Working Session — 2026-03-14, item 7; Hypothesis H-012: tenant-wide enablement extends to sandbox capacity by default}
- If **Copilot** enabled at tenant level → FABRIC_SANDBOX_USERS could use Copilot in DEV-PLAYGROUND; this is outside the finance-workspace CAB requirement scope (PD-001 scopes to finance-associated workspaces). {Hypothesis H-013: sandbox Copilot enablement is not explicitly blocked; CAB gate applies to finance-associated workspaces specifically; Confidence: Medium}
**Cascade-on-feature-disable:**
- If **F64-SANDBOX capacity** is reassigned or reduced → FABRIC_SANDBOX_USERS lose their experimentation environment entirely; wave 2 testing capability is eliminated. {Evidence: CAB Minutes — 2026-03-21, item 1; Hypothesis H-007}
**Risk-if-misconfigured:** High — if sandbox users are granted access to silver or gold workspaces, the PII segregation boundary (L-007) is breached and production finance data becomes accessible in an uncontrolled environment.
**Recommended-pre-rollout-check:** Confirm FABRIC_SANDBOX_USERS has no workspace membership in FIN-GLD-REPORTING, FIN-EXEC-DASH, or SILVER-OPS; validate no production finance datasets are published to DEV-PLAYGROUND.
**Tags:** {Evidence: CAB Minutes — 2026-03-21, items 1–2; Hypothesis H-001, H-007, H-012, H-013}
---
**HIGH_RISK_GROUPS:** FABRIC_FINANCE_ADMINS, FABRIC_SANDBOX_USERS
**GROUPS_REQUIRING_NEW_SUBGROUPS:**
- FABRIC_FINANCE_ADMINS — likely needs splitting into workspace-scoped subgroups (e.g., FABRIC_FINANCE_ADMINS_GLD_REPORTING, FABRIC_FINANCE_ADMINS_EXEC_DASH) to allow granular Copilot and feature enablement per workspace rather than across both gold workspaces simultaneously. {Hypothesis H-014: standard Fabric governance pattern where a single admin group spanning multiple workspaces prevents granular feature gating; Premise: PD-001 requires CAB approval per finance workspace; Premise: a single group cannot be selectively applied per workspace without subgroup splitting; Confidence: High}
- FABRIC_FINANCE_VIEWERS — may require a subgroup for SILVER-OPS access if viewer populations differ between gold and silver tiers; currently no documented separation. {Hypothesis H-015: Confidence: Low — insufficient evidence in inputs to confirm viewer population differs across tiers}
---
# PHASE 5: RISK SURFACE MAP
## SURFACE A — Capacity Risk
**Capacity: F256-PROD-FINANCE**
- Risk: SAP migration timeline extension keeps gold-tier workspaces locked to F256 beyond planned wave 2 window; capacity cannot be resized without violating L-001.
- Severity: 4 | Likelihood: 3 | CISC-score: 12
- Mitigation-direction: Define SAP migration completion criteria and communicate them to the CAB as the F256 lock release trigger.
- Tag: {Evidence: Governance Working Session — 2026-03-14, item 1}
**Capacity: F256-PROD-FINANCE**
- Risk: FIN-EXEC-DASH manager unknown; no named accountable owner to approve changes to this workspace's configuration on F256.
- Severity: 3 | Likelihood: 4 | CISC-score: 12
- Mitigation-direction: Identify and assign a workspace manager for FIN-EXEC-DASH before wave 2 initiation.
- Tag: {Evidence: Architectural Artefact — Workspace Inventory, row 2; Gap G-002}
**Capacity: F128-ANALYTICS**
- Risk: SILVER-HR is assigned to F128-ANALYTICS but absent from the Workspace Inventory; its governance status, tier, and data classification are unknown.
- Severity: 3 | Likelihood: 4 | CISC-score: 12
- Mitigation-direction: Confirm SILVER-HR existence, tier, and governance ownership; add to Workspace Inventory.
- Tag: {Gap G-001; Hypothesis H-006}
**Capacity: F64-SANDBOX**
- Risk: FABRIC_SANDBOX_USERS granted access to production finance datasets published to DEV-PLAYGROUND, breaching L-007.
- Severity: 5 | Likelihood: 2 | CISC-score: 10
- Mitigation-direction: Audit DEV-PLAYGROUND for any datasets sourced from or containing production PII data; enforce ingestion controls.
- Tag: {Evidence: CAB Minutes — 2026-03-21, item 2; Hypothesis H-001}
---
## SURFACE B — Workspace Tier Risk
**Tier: Gold (FIN-GLD-REPORTING, FIN-EXEC-DASH)**
- Risk: FIN-EXEC-DASH has no source control; L-005 blocks wave 2 migration for this workspace; delay propagates to Finance-Prod-Pipeline dependency.
- Severity: 5 | Likelihood: 5 | CISC-score: 25
- Mitigation-direction: Initiate Azure DevOps repository connection for FIN-EXEC-DASH immediately; treat as wave 2 blocking item.
- Tag: {Evidence: CAB Minutes — 2026-03-21, item 3; Architectural Artefact — Source Control section}
**Tier: Gold (FIN-GLD-REPORTING, FIN-EXEC-DASH)**
- Risk: External guest sharing prohibition (L-004) is not enforced through a documented technical control; reliance on policy awareness alone creates access creep risk.
- Severity: 4 | Likelihood: 3 | CISC-score: 12
- Mitigation-direction: Confirm tenant-level external sharing toggle is set to OFF for gold-tier workspaces or that workspace-level controls enforce L-004 technically, not just procedurally.
- Tag: {Evidence: Governance Working Session — 2026-03-14, item 3}
**Tier: Gold**
- Risk: On-prem gateway SSRS dependency in gold-tier workspaces creates a brittle refresh path; gateway failure or maintenance window causes production finance reporting outage.
- Severity: 4 | Likelihood: 3 | CISC-score: 12
- Mitigation-direction: Document which specific SSRS datasets and workspaces depend on the gateway; establish a gateway health monitoring baseline.
- Tag: {Evidence: Governance Working Session — 2026-03-14, item 5; Hypothesis H-005}
**Tier: Silver (SILVER-OPS)**
- Risk: SILVER-HR governance gap (absent from Workspace Inventory) means F128-ANALYTICS capacity governance is partially blind; an ungoverned workspace on a shared capacity creates an unmonitored data access surface.
- Severity: 3 | Likelihood: 4 | CISC-score: 12
- Mitigation-direction: Add SILVER-HR to the governed workspace inventory; assign a manager and AD group.
- Tag: {Hypothesis H-006; Gap G-001}
**Tier: Bronze (DEV-PLAYGROUND)**
- Risk: Git integration permitted under P-002 (Azure DevOps only); if configured with the wrong provider or without enforced branch policies, non-production artifacts could propagate to connected repos.
- Severity: 2 | Likelihood: 2 | CISC-score: 4
- Mitigation-direction: Enforce Azure DevOps branch protection policies on any repo connected to DEV-PLAYGROUND before enabling Git integration.
- Tag: {Evidence: Governance Working Session — 2026-03-14, item 4}
---
## SURFACE C — Feature Enablement Risk
**Feature: Copilot**
- Risk: Copilot enabled in FIN-GLD-REPORTING or FIN-EXEC-DASH before CAB approval; AI-generated outputs over production finance data exposed to workspace members without governance sign-off.
- Severity: 5 | Likelihood: 2 | CISC-score: 10
- Mitigation-direction: Confirm Copilot is technically disabled at capacity (F256-PROD-FINANCE) or workspace level for both gold-tier finance workspaces; do not rely on process gate alone.
- Tag: {Evidence: Governance Working Session — 2026-03-14, item 2}
**Feature: Fabric Data Activator**
- Risk: Tenant-wide enablement decision pending (PD-002); if enabled without a governance owner for finance scope, event-driven actions could trigger automated processes on finance data without audit trail.
- Severity: 3 | Likelihood: 2 | CISC-score: 6
- Mitigation-direction: Do not enable Data Activator tenant-wide until the pending decision is resolved and a finance-scoped governance owner is assigned.
- Tag: {Evidence: Governance Working Session — 2026-03-14, item 7}
**Feature: Tenant-Level Sharing Links**
- Risk: Re-enabled without CAB review, reversing an audit remediation; finance reports distributed via sharing links would bypass L-004 guest sharing prohibition.
- Severity: 4 | Likelihood: 2 | CISC-score: 8
- Mitigation-direction: Maintain OFF state; route any re-enablement request through CAB with explicit audit remediation sign-off.
- Tag: {Evidence: CAB Minutes — 2026-03-21, item 4}
**Feature: Fabric Git Integration (gold-tier)**
- Risk: Git integration required for wave 2 (L-005) but not yet configured for FIN-EXEC-DASH; delayed configuration blocks the wave 2 CAB gate.
- Severity: 5 | Likelihood: 5 | CISC-score: 25
- Mitigation-direction: Treat FIN-EXEC-DASH source control configuration as a wave 2 pre-condition; assign Sarah Chen or the FIN-EXEC-DASH manager as accountable owner once identified.
- Tag: {Evidence: CAB Minutes — 2026-03-21, item 3; Architectural Artefact — Source Control section}
**Feature: Legacy SSRS / On-Prem Gateway**
- Risk: No documented migration timeline for legacy SSRS datasets; if gateway is decommissioned as part of modernization without migrating these datasets first, production finance refresh breaks.
- Severity: 5 | Likelihood: 3 | CISC-score: 15
- Mitigation-direction: Enumerate all gateway-dependent SSRS datasets and their hosting workspaces; create a migration backlog item before wave 2 scope is finalized.
- Tag: {Evidence: Governance Working Session — 2026-03-14, item 5; Hypothesis H-005}
---
## SURFACE D — Process Risk (CAB / Change Mgmt / CICD)
**Process: Wave 2 source control gate**
- Risk: CAB gate (L-005) requires source control for all production semantic models before wave 2 proceeds; FIN-EXEC-DASH is non-compliant and its manager is unknown, making remediation ownership unclear.
- Severity: 5 | Likelihood: 4 | CISC-score: 20
- Mitigation-direction: Assign a named accountable owner for FIN-EXEC-DASH; escalate source control gap to CAB as a pre-wave-2 blocking item.
- Tag: {Evidence: CAB Minutes — 2026-03-21, item 3; Gap G-002}
**Process: Workspace ownership violation**
- Risk: Multiple workspaces exceed documented ownership limits (AM-002); unowned workspaces cannot be governed through change control, creating untracked change risk in a wave 2 migration.
- Severity: 3 | Likelihood: 4 | CISC-score: 12
- Mitigation-direction: Conduct a workspace ownership audit across all inventoried workspaces before wave 2 begins; remediate violations through AD group assignments.
- Tag: {Evidence: Governance Working Session — 2026-03-14, item 11; Hypothesis H-004}
**Process: Legacy-PBI-Deploy coexistence**
- Risk: Wave 2 migration runs in parallel with Legacy-PBI-Deploy (active until Q4); conflicting deployment pipeline states for overlapping workspaces could cause race conditions or overwrite Fabric-managed deployments.
- Severity: 4 | Likelihood: 3 | CISC-score: 12
- Mitigation-direction: Map Legacy-PBI-Deploy's workspace targets; confirm it does not overlap with Finance-Prod-Pipeline targets during wave 2 migration window.
- Tag: {Evidence: Governance Working Session — 2026-03-14, item 8; Architectural Artefact — Pipelines section}
**Process: Architecture review bypass risk**
- Risk: Teams have already requested GitHub Enterprise integration despite the architecture review not approving it (PR-001); informal workarounds (e.g., personal access tokens to GitHub) could be attempted outside governance visibility.
- Severity: 3 | Likelihood: 2 | CISC-score: 6
- Mitigation-direction: Enforce Azure DevOps-only Git provider at the tenant level if the Fabric admin toggle supports it; communicate PR-001 to all workspace managers.
- Tag: {Evidence: Governance Working Session — 2026-03-14, item 9}
---
**TOP_5_RISKS_BY_CISC:**
| Rank | Risk | CISC | Surface |
|------|------|------|---------|
| 1 | FIN-EXEC-DASH source control absent — wave 2 migration blocked | 25 | B + C |
| 2 | Wave 2 CAB gate non-compliance — FIN-EXEC-DASH owner unknown | 20 | D |
| 3 | Legacy SSRS / on-prem gateway — no migration path defined | 15 | C |
| 4 (tied) | F256-PROD-FINANCE lock — SAP timeline extension risk | 12 | A |
| 4 (tied) | F256-PROD-FINANCE — FIN-EXEC-DASH manager unknown | 12 | A |
| 4 (tied) | F128-ANALYTICS — SILVER-HR governance gap | 12 | A + B |
| 4 (tied) | Gold-tier external sharing — no technical enforcement confirmed | 12 | B |
| 4 (tied) | Workspace ownership violations — untracked change risk | 12 | D |
| 4 (tied) | Legacy-PBI-Deploy coexistence — pipeline race condition risk | 12 | D |
**RISKS_REQUIRING_CAB_NOTIFICATION:**
- FIN-EXEC-DASH source control gap (wave 2 blocking — L-005)
- Workspace ownership violations (AM-002 — multiple workspaces affected)
- Legacy-PBI-Deploy coexistence with wave 2 pipeline (L-008 / pipeline overlap)
- Copilot enablement status confirmation (PD-001 gate)
- Fabric Data Activator pending decision (PD-002)
---
# PHASE 6: INFERENCE LOG (MASTER AUDIT TRAIL)
| Inference-ID | H-001 |
|---|---|
| Phase-of-origin | 1 |
| Inference-statement | FABRIC_SANDBOX_USERS is scoped to DEV-PLAYGROUND / F64-SANDBOX. |
| Reasoning-chain | Premise: The group name contains "SANDBOX". Premise: F64-SANDBOX is the only sandbox capacity in the inventory. Premise: DEV-PLAYGROUND is the only workspace assigned to F64-SANDBOX. Conclusion: The group's access scope is DEV-PLAYGROUND. |
| Evidence-anchors | Architectural Artefact — AD Groups row 3; Capacity Inventory row 3; Workspace Inventory row 4 |
| Confidence | High |
| Falsifiability | Explicit documentation showing FABRIC_SANDBOX_USERS assigned to non-sandbox workspaces would falsify this. |
| Risk-if-wrong | FABRIC_SANDBOX_USERS may have broader access, invalidating PII segregation analysis. |
| Inference-ID | H-002 |
|---|---|
| Phase-of-origin | 1 |
| Inference-statement | Finance-Prod-Pipeline requires migration as part of wave 2. |
| Reasoning-chain | Premise: L-005 requires all production semantic models to have source control before wave 2. Premise: Finance-Prod-Pipeline targets prod-only. Premise: Production semantic models in FIN-GLD-REPORTING and FIN-EXEC-DASH are in scope. Conclusion: The pipeline, which deploys these models, is directly implicated in wave 2 migration. |
| Evidence-anchors | CAB Minutes — 2026-03-21, item 3; Architectural Artefact — Pipelines section, row 1 |
| Confidence | High |
| Falsifiability | Documentation showing Finance-Prod-Pipeline targets workspaces outside wave 2 scope would reduce the migration requirement. |
| Risk-if-wrong | Pipeline migration may not be required; planning effort is misdirected. |
| Inference-ID | H-003 |
|---|---|
| Phase-of-origin | 2 |
| Inference-statement | Azure DevOps-only Git constraint applies across all workspace tiers, not just bronze. |
| Reasoning-chain | Premise: GitHub Enterprise is the only named alternative Git provider. Premise: GitHub Enterprise is not approved by architecture review. Premise: No other Git providers are mentioned in inputs. Conclusion: Azure DevOps is the only available Git provider for any tier. |
| Evidence-anchors | Governance Working Session — 2026-03-14, items 4 and 9 |
| Confidence | Medium |
| Falsifiability | Explicit approval of another Git provider (other than GitHub Enterprise) for silver or gold tiers would falsify this. |
| Risk-if-wrong | Silver or gold workspaces might attempt to connect an unapproved Git provider, creating an ungoverned source control path. |
| Inference-ID | H-004 |
|---|---|
| Phase-of-origin | 2 |
| Inference-statement | FIN-EXEC-DASH is among the workspaces exceeding documented ownership limits. |
| Reasoning-chain | Premise: Multiple workspaces exceed ownership limits (AM-002). Premise: FIN-EXEC-DASH has no named manager in the Architectural Artefact. Premise: Unassigned manager = likely ownership limit violation. Conclusion: FIN-EXEC-DASH is a probable violator. |
| Evidence-anchors | Governance Working Session — 2026-03-14, item 11; Architectural Artefact — Workspace Inventory, row 2 |
| Confidence | Medium |
| Falsifiability | Ownership limit documentation defining what constitutes a "limit" (e.g., max workspaces per person) would either confirm or exclude FIN-EXEC-DASH as a violator. |
| Risk-if-wrong | FIN-EXEC-DASH may be compliant; the real violators are elsewhere and remain unidentified. |
| Inference-ID | H-005 |
|---|---|
| Phase-of-origin | 2 |
| Inference-statement | Legacy SSRS datasets on on-prem gateway are hosted in FIN-GLD-REPORTING. |
| Reasoning-chain | Premise: The SSRS gateway concern was raised in a finance governance session. Premise: FIN-GLD-REPORTING is the primary production financial reporting workspace. Premise: On-prem gateway dependencies for finance reporting most likely reside in the primary production workspace. Conclusion: FIN-GLD-REPORTING is the probable host for gateway-dependent datasets. |
| Evidence-anchors | Governance Working Session — 2026-03-14, item 5; Architectural Artefact — Workspace Inventory, row 1 |
| Confidence | Medium |
| Falsifiability | A dataset inventory showing gateway-dependent SSRS datasets assigned to workspaces other than FIN-GLD-REPORTING would falsify or refine this. |
| Risk-if-wrong | Gateway dependency may span multiple workspaces; risk is underestimated if FIN-EXEC-DASH or SILVER-OPS also depend on the gateway. |
| Inference-ID | H-006 |
|---|---|
| Phase-of-origin | 1 |
| Inference-statement | SILVER-HR exists as an active workspace in the tenant. |
| Reasoning-chain | Premise: F128-ANALYTICS capacity inventory explicitly lists SILVER-HR as an assigned workspace. Premise: Fabric capacity assignments require the workspace to exist. Conclusion: SILVER-HR is a live workspace omitted from the Workspace Inventory document. |
| Evidence-anchors | Architectural Artefact — Capacity Inventory, row 2 |
| Confidence | High |
| Falsifiability | A confirmation that SILVER-HR is decommissioned and the capacity inventory is stale would falsify this. |
| Risk-if-wrong | Capacity inventory is inaccurate; F128-ANALYTICS governance analysis based on it is unreliable. |
| Inference-ID | H-007 |
|---|---|
| Phase-of-origin | 2 |
| Inference-statement | All bronze-tier constraints in scope apply exclusively to DEV-PLAYGROUND within wave 2. |
| Reasoning-chain | Premise: DEV-PLAYGROUND is the only bronze-tier workspace in the Workspace Inventory. Premise: No other bronze-tier workspaces are named in any input. Conclusion: Bronze-tier constraints map solely to DEV-PLAYGROUND for this analysis. |
| Evidence-anchors | Architectural Artefact — Workspace Inventory |
| Confidence | High |
| Falsifiability | Discovery of additional bronze-tier workspaces not in the inventory would broaden applicability. |
| Risk-if-wrong | Additional ungoverned bronze-tier workspaces may exist and are not covered by this analysis. |
| Inference-ID | H-008 |
|---|---|
| Phase-of-origin | 2 |
| Inference-statement | FABRIC_FINANCE_ADMINS is the designated AD group for admin access to gold-tier finance workspaces. |
| Reasoning-chain | Premise: L-002 mandates admin rights must route through AD groups only. Premise: FABRIC_FINANCE_ADMINS is the only finance-scoped admin group in the inventory. Premise: Gold-tier finance workspaces require admin access. Conclusion: FABRIC_FINANCE_ADMINS is the required vehicle for admin assignment to FIN-GLD-REPORTING and FIN-EXEC-DASH. |
| Evidence-anchors | Governance Working Session — 2026-03-14, item 6; Architectural Artefact — AD Groups |
| Confidence | High |
| Falsifiability | Discovery of additional finance-scoped admin groups not in the inventory would complicate or supplant this inference. |
| Risk-if-wrong | A different, undocumented group may hold admin access, leaving FABRIC_FINANCE_ADMINS with insufficient authority to govern wave 2 changes. |
| Inference-ID | H-009 |
|---|---|
| Phase-of-origin | 3 |
| Inference-statement | F128-ANALYTICS capacity reassignment is not blocked by the SAP migration lock. |
| Reasoning-chain | Premise: L-001 locks only "production financial reporting workspaces" on F256. Premise: SILVER-OPS and SILVER-HR are on F128-ANALYTICS. Premise: Silver-tier workspaces are not classified as production financial reporting workspaces in the inputs. Conclusion: F128 is not subject to the SAP migration lock. |
| Evidence-anchors | Governance Working Session — 2026-03-14, item 1; Architectural Artefact — Capacity Inventory |
| Confidence | Medium |
| Falsifiability | Documentation classifying SILVER-OPS or SILVER-HR as finance-reporting workspaces subject to the same lock would falsify this. |
| Risk-if-wrong | Reassigning F128 capacity could violate an undocumented constraint; silver-tier governance is disrupted. |
| Inference-ID | H-010 |
|---|---|
| Phase-of-origin | 4 |
| Inference-statement | FABRIC_FINANCE_ADMINS bears default accountability for new tenant-level features enabled in finance workspaces. |
| Reasoning-chain | Premise: FABRIC_FINANCE_ADMINS is the admin group for finance workspaces (H-008). Premise: No other governance owner is named for finance-scoped feature management. Premise: Admin groups in Fabric inherit management responsibilities for features enabled in their workspaces. Conclusion: Feature enablement accountability defaults to FABRIC_FINANCE_ADMINS in the absence of a named alternative. |
| Evidence-anchors | Architectural Artefact — AD Groups; Governance Working Session — 2026-03-14, items 2 and 7 |
| Confidence | Medium |
| Falsifiability | A named feature governance owner outside FABRIC_FINANCE_ADMINS would transfer accountability. |
| Risk-if-wrong | Accountability gap remains; new features are enabled without a responsible owner, creating ungoverned change. |
| Inference-ID | H-011 |
|---|---|
| Phase-of-origin | 4 |
| Inference-statement | Copilot access in finance workspaces, if enabled, extends to FABRIC_FINANCE_VIEWERS members at viewer permission level. |
| Reasoning-chain | Premise: Copilot in Fabric surfaces AI-generated content to workspace members at their permission level. Premise: FABRIC_FINANCE_VIEWERS holds viewer-level membership in finance workspaces. Premise: Viewer-level Copilot access exposes AI-generated summaries over workspace data. Conclusion: Enabling Copilot without restricting viewer access would extend Copilot outputs to FABRIC_FINANCE_VIEWERS. |
| Evidence-anchors | Governance Working Session — 2026-03-14, item 2; Architectural Artefact — AD Groups |
| Confidence | Medium |
| Falsifiability | Fabric Copilot documentation confirming that viewer access is excluded from Copilot features would falsify this. |
| Risk-if-wrong | Viewer exposure is not a concern; Copilot risk is limited to higher-permission members only. |
| Inference-ID | H-012 |
|---|---|
| Phase-of-origin | 4 |
| Inference-statement | Tenant-wide Data Activator enablement extends to F64-SANDBOX and DEV-PLAYGROUND by default. |
| Reasoning-chain | Premise: PD-002 frames Data Activator as a tenant-wide enablement decision. Premise: Tenant-wide toggles in Fabric apply to all capacities unless capacity-level overrides exist. Premise: No capacity-level override for F64-SANDBOX is mentioned in any input. Conclusion: Tenant-wide enablement includes DEV-PLAYGROUND. |
| Evidence-anchors | Governance Working Session — 2026-03-14, item 7 |
| Confidence | Medium |
| Falsifiability | Fabric documentation or tenant configuration showing Data Activator can be restricted to specific capacities at enablement would reduce or eliminate sandbox exposure. |
| Risk-if-wrong | Sandbox is not affected; Data Activator scope analysis for FABRIC_SANDBOX_USERS is irrelevant. |
| Inference-ID | H-013 |
|---|---|
| Phase-of-origin | 4 |
| Inference-statement | Copilot enablement in DEV-PLAYGROUND (sandbox) is not blocked by PD-001. |
| Reasoning-chain | Premise: PD-001 requires CAB approval for Copilot in "finance-associated workspaces." Premise: DEV-PLAYGROUND is a bronze-tier sandbox, not classified as finance-associated in the inputs. Conclusion: The CAB gate for Copilot does not extend to DEV-PLAYGROUND. |
| Evidence-anchors | Governance Working Session — 2026-03-14, item 2; Architectural Artefact — Workspace Inventory, row 4 |
| Confidence | Medium |
| Falsifiability | Documentation defining "finance-associated workspace" to include DEV-PLAYGROUND (e.g., if finance datasets are present there) would extend the CAB gate to the sandbox. |
| Risk-if-wrong | Copilot activated in DEV-PLAYGROUND requires CAB approval; sandbox experimentation is blocked until approval is obtained. |
| Inference-ID | H-014 |
|---|---|
| Phase-of-origin | 4 |
| Inference-statement | FABRIC_FINANCE_ADMINS requires splitting into workspace-scoped subgroups to support granular per-workspace feature gating. |
| Reasoning-chain | Premise: PD-001 requires CAB approval per finance-associated workspace for Copilot. Premise: A single AD group spanning FIN-GLD-REPORTING and FIN-EXEC-DASH cannot be selectively applied to one workspace without applying to both. Premise: Wave 2 migration may require staged feature enablement per workspace. Conclusion: Subgroup splitting is needed to support workspace-level governance differentiation. |
| Evidence-anchors | Governance Working Session — 2026-03-14, item 2; Architectural Artefact — AD Groups and Workspace Inventory |
| Confidence | High |
| Falsifiability | Fabric workspace-level feature toggle capability (independent of AD group structure) that allows per-workspace Copilot control without AD subgroup splitting would falsify this. |
| Risk-if-wrong | Subgroup splitting is unnecessary; single group can be used without governance loss. |
| Inference-ID | H-015 |
|---|---|
| Phase-of-origin | 4 |
| Inference-statement | FABRIC_FINANCE_VIEWERS may need a subgroup for SILVER-OPS if viewer populations differ across tiers. |
| Reasoning-chain | Premise: FABRIC_FINANCE_VIEWERS is a single group with no tier-based scope documented. Premise: Gold-tier and silver-tier data sensitivity may differ. Conclusion: If viewer populations differ, a single group creates access creep risk across tiers. |
| Evidence-anchors | Architectural Artefact — AD Groups; Workspace Inventory |
| Confidence | Low |
| Falsifiability | Confirmation that the same viewer population requires access to both gold and silver workspaces would remove the need for splitting. |
| Risk-if-wrong | Unnecessary subgroup splitting adds AD management overhead without governance benefit. |
---
# PHASE 7: GAP REGISTRY
| Gap-ID | G-001 |
|---|---|
| Gap-statement | SILVER-HR workspace is referenced in the capacity inventory but absent from the Workspace Inventory; its tier, manager, AD group assignments, and governance status are unknown. |
| Phase-of-origin | 1 |
| Why-it-matters | SILVER-HR may contain HR-classified data on a shared capacity (F128-ANALYTICS); its absence from the inventory means it is ungoverned within this analysis. Any wave 2 governance framework built on the current inventory is incomplete. |
| Suggested-source | Fabric Admin portal — workspace list export; HR data platform team for ownership confirmation. |
| Severity | Blocking |
| Gap-ID | G-002 |
|---|---|
| Gap-statement | FIN-EXEC-DASH has no named manager; accountability for wave 2 source control configuration and CAB gate compliance is unassigned. |
| Phase-of-origin | 1 |
| Why-it-matters | L-005 requires source control before wave 2; without an owner, the remediation has no accountable executor. The CAB gate cannot be closed without a named responsible party. |
| Suggested-source | Finance leadership / workspace provisioning records to identify who requested FIN-EXEC-DASH. |
| Severity | Blocking |
| Gap-ID | G-003 |
|---|---|
| Gap-statement | DEV-PLAYGROUND has no named manager. |
| Phase-of-origin | 1 |
| Why-it-matters | Git integration configuration and PII segregation enforcement in the sandbox require an accountable owner. Without one, sandbox governance operates without a responsible party. |
| Suggested-source | IT provisioning records or FABRIC_SANDBOX_USERS group owner. |
| Severity | Important |
| Gap-ID | G-004 |
|---|---|
| Gap-statement | Source control configuration status for FIN-GLD-REPORTING is not documented. The Architectural Artefact only confirms Azure DevOps for SILVER-OPS and confirms the absence for FIN-EXEC-DASH; FIN-GLD-REPORTING's status is unaddressed. |
| Phase-of-origin | 1 |
| Why-it-matters | L-005 requires all production semantic models to have source control before wave 2. If FIN-GLD-REPORTING is also non-compliant, the blocking risk doubles and the wave 2 gate is further at risk. |
| Suggested-source | Sarah Chen (FIN-GLD-REPORTING manager) or Fabric Admin portal Git integration settings. |
| Severity | Blocking |
| Gap-ID | G-005 |
|---|---|
| Gap-statement | Legacy-PBI-Deploy target environments and workspace assignments are not documented; it is unknown whether this pipeline targets workspaces that overlap with Finance-Prod-Pipeline's scope. |
| Phase-of-origin | 1 |
| Why-it-matters | If Legacy-PBI-Deploy and Finance-Prod-Pipeline share workspace targets, parallel operation during wave 2 creates a pipeline race condition risk (Surface D risk). |
| Suggested-source | Power BI / Fabric deployment pipeline configuration export; pipeline owner or DevOps team. |
| Severity | Important |
| Gap-ID | G-006 |
|---|---|
| Gap-statement | No migration path, timeline, or ownership is defined for legacy SSRS datasets dependent on the on-prem gateway. |
| Phase-of-origin | 3 |
| Why-it-matters | If the on-prem gateway is decommissioned as part of the modernization initiative without migrating these datasets first, production finance reporting breaks. The wave 2 migration plan cannot be finalized without knowing the gateway dependency scope. |
| Suggested-source | Finance data engineering team; gateway administrator; SSRS report inventory. |
| Severity | Blocking |
| Gap-ID | G-007 |
|---|---|
| Gap-statement | The definition of "documented ownership limits" referenced in the governance session (AM-002) is not provided; the specific workspaces in violation are not named. |
| Phase-of-origin | 2 |
| Why-it-matters | Without knowing which workspaces are in violation and what the limit definition is, ownership remediation cannot be scoped or prioritized for wave 2. |
| Suggested-source | Governance policy document referenced in the working session; Fabric Admin workspace report (workspace owner field). |
| Severity | Important |
| Gap-ID | G-008 |
|---|---|
| Gap-statement | The exact membership of FABRIC_FINANCE_ADMINS and FABRIC_FINANCE_VIEWERS is not documented; it is unknown whether direct individual admin assignments currently exist in violation of L-002. |
| Phase-of-origin | 2 |
| Why-it-matters | If direct individual admin assignments exist in addition to group-based access, L-002 is currently in violation. Wave 2 migration on top of a non-compliant access state creates audit exposure. |
| Suggested-source | Azure Active Directory group membership export; Fabric workspace permissions audit. |
| Severity | Blocking |
---
*Intelligence package complete. All Hypothesis tags migrated to Phase 6 Inference Log. All Gap tags migrated to Phase 7 Gap Registry. No recommendations or strategy content included. Output is structured for consumption by Prompt 2 (CAB-defensible Phase-In Strategy).*
By purchasing this prompt, you agree to our terms of service
CLAUDE-4-6-SONNET
This is not a summarizer.
It is a governance reasoning system built for consultants, Fabric architects, enterprise platform teams, and governance reviewers who need defensible outputs before migration or feature rollout decisions.
Every extracted claim is automatically tagged as:
{Evidence} → directly supported by source inputs
{Hypothesis} → inferred with explicit reasoning chain
{Gap} → missing information requiring validation
...more
Added 3 weeks ago
- Reviews for this prompt (1)